South Korea used to take great pride in its Public Key Infrastructure (PKI) implementation. Government officials could no doubt parade impressive ‘numbers’ and ‘achievements.’ As of 2016, for example, more than 35 million user certificates were issued by the Certification Authority (CA) accredited by the government under the Korean National PKI regime (“NPKI”). Korean NPKI has been in existence since 1999 in isolation from the rest of the world. Almost all internet banking, e-commerce providers and e-government agencies in Korea require users to present user certificates (issued by an NPKI accredited CA) for authentication purpose and to ensure integrity of transaction records (transaction confirmation). No other countries that I know of have achieved this level of adoption of PKI technology at the client side.
All this started in the late 1990’s. Government funded researchers succeeded in developing a high-grade encryption algorithm (128 bit encryption, which was state-of-the-art in 1990s). A handful of companies came up with prototype PKI implementations for client authentication and transaction confirmation using web-browser plugins incorporating the Korean-developed high-grade encryption algorithm. Government officials were impressed with the achievements. They thought the technology would have great potential for e-commerce (which was at its nascent stage then) and e-government services as well as nationwide online identity infrastructure. Scholars were commissioned to produce consultation papers recommending legislation, 1) to introduce governmental scrutiny to ensure the security of the NPKI certification service; and 2) to grant the privileged status on government-accredited CAs.
As a result, the 1999 Digital Signature Act was introduced in Korea. It stipulates that where signature is required by law, in order to satisfy such a legal requirement electronically, one has to use the certificate issued by an NPKI accredited CA. No other electronic signatures, no matter how secure, reliable or appropriate, can meet the legal requirement for a signature under the Korean law. This outright ‘legal’ and systematic institutional discrimination of foreign or non-accredited Korean CAs and the preferential treatment of government accredited Korean CAs are in many ways against the UNCITRAL Model Law on Electronic Signatures. Art 3 of the Model Law stipulates that signatures must be treated equally provided that they are equally reliable (Art. 3). Art 12 of the Model Law requires global recognition of a certificate or an electronic signature regardless of the geographical location of the issuer of the certificate or the user (the signatory). The “national” regime of Korean NPKI which confers the legal effect only on the electronic signatures created using a certificate issued by an NPKI accredited CA located in Korea is against these clauses of the Model Law and resulted in a self-imposed isolation of the Korean NPKI.
Moreover, the Korean legal approach which confers a privileged status on its “national” PKI implementation and denies legal effect to all other implementations of electronic signatures is an anomaly compared to the European Union (EU) E-Signature Directive 1999 and Electronic Identification, Authentication and Trust Services (eIDAS) Regulation 2014. The EU legal approaches to electronic signatures are “inclusive” in the sense that they do not purport to deprive legal effect of any electronic signatures merely on the ground that they do not meet the requirements of qualified electronic signatures. The US state laws, which are mostly based on the Uniform Electronic Transactions Act 1999, are also inclusive in the sense that electronic signatures, regardless of their reliability, are not denied legal effect merely on the ground that they are in electronic form. But the Korean Electronic Signature Act confers legal effect only on electronic signatures created using a certificate issued by an NPKI CA located in Korea. No other electronic signatures may have a comparable legal status in Korea.
 Boosted and protected by this peculiar legal regime, five or six NPKI accredited CAs have been in operation in Korea for the past two decades in isolation from the rest of the world. All these NPKI accredited CAs use more or less the same technology. They claim that they have standardized the client side PKI implementation and achieved interoperability. Which means that as long as you have your user certificate issued by one of the NPKI accredited CAs, it will not be difficult to use it for e-commerce or e-government transactions–provided that you use the supported web-browser or you installed an appropriate mobile app. All this, however, started from the government initiative to supervise the NPKI certification service and to grant special privileges to the NPKI accredited CAs.
Boosted and protected by this peculiar legal regime, five or six NPKI accredited CAs have been in operation in Korea for the past two decades in isolation from the rest of the world. All these NPKI accredited CAs use more or less the same technology. They claim that they have standardized the client side PKI implementation and achieved interoperability. Which means that as long as you have your user certificate issued by one of the NPKI accredited CAs, it will not be difficult to use it for e-commerce or e-government transactions–provided that you use the supported web-browser or you installed an appropriate mobile app. All this, however, started from the government initiative to supervise the NPKI certification service and to grant special privileges to the NPKI accredited CAs.
Inside Korea, the Korean NPKI certification service has become ubiquitous and it certainly feels like a “standard” technology. But once you leave Korea, the technology and the services are hardly known. They are, for all practical purposes, un-workable for non-Koreans and even for Koreans outside Korea. Indeed, this piece of technology (as it is used for user authentication and transaction confirmation) is the one which isolates Korean e-commerce from the rest of the world as it prevents Korean e-commerce providers from reaching out to customers in the rest of the world.
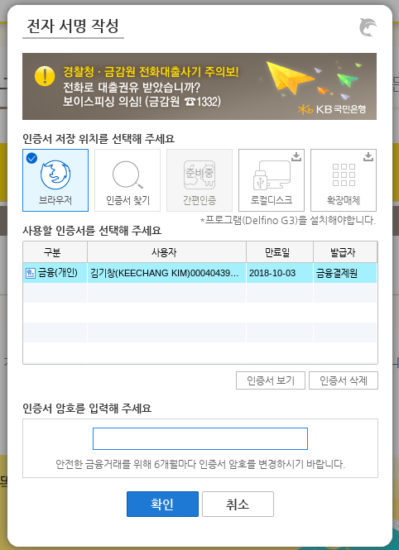
But most of all, there are serious security vulnerabilities of the Korean NPKI implementation of user authentication and transaction confirmation. As the accredited CAs routinely “re-issue” user certificates online without face-to-face verification of the applicant’s identity, phishing attacks to obtain user credentials needed to obtain user certificates through online application/issuance became rampant. Every year, thousands of successful phishing attacks are reported but the banks are allowed to put the blame squarely on the so-called “gross negligence” of the users, who were merely victims of carefully orchestrated attacks. As far as negligence or gross negligence is concerned, I believe that the banks are far more negligent or even grossly negligent because they have knowingly persisted in using the method whose weakness to phishing attacks is fully documented already. Unfortunately, Korean judges do not agree and they side with the banks rather than with the victims of the phishing attacks.
Compared to “FIDO” (Fast Identity Online), the industry standard for online authentication which started in 2013 and is currently in active development and adoption worldwide, the Korean NPKI’s implementation backwardness and vulnerabilities are all the more striking. The creative breakthrough underpinning FIDO standard is to distinguish and insulate “user interaction scenario” from “authentication process.” The former occurs on a given device and stays within the device. The latter occurs online between the device and the service provider. This can ensure interoperability of FIDO standard across a wide range of devices and the user interaction scenario can accommodate a variety of user-friendly authentication methods without compromising the “authentication process” which is insulated from the “user interaction scenario.” Moreover, the authentication process under FIDO standard requires that a key issued to a particular website can only be exercised by that website. So phishing attempts to acquire the authentication key become useless. In stark contrast, the NPKI authentication process relies on a user certificate which can open all the doors to the websites the user is registered with. According to a recent Korean Supreme Court ruling, an attacker who has fraudulently obtained a user certificate issued by an NPKI accredited CA can even open up new accounts with any financial companies and start borrowing money in the name of the victim. This is indeed an attackers’ heaven! But when a particular authentication technology is described in the statute book as “secure” or “reliable,” judges are bound to show deference to the power of “words” and “provisions” rather than understanding the vulnerable realities of a complicated technology. The Korean NPKI regime is grounded on a technology which is inherently and conceptually more vulnerable compared to FIDO standard. But it enjoys a statutory backing dating back from 1999.
 An old technology of the late 1990s proving to be less secure than the cutting-edge security standards of the 2010s should not surprise anyone because the technology progresses and improves. But the problem with a government driven ‘standard’ is that once such a government driven regime is put in place, it becomes authoritative and remarkably difficult to get rid of. After nearly two decades, the Korean government, as well as its citizens, are still stuck with the outdated authentication concept and process of NPKI client authentication. Some of those who have vested interests in the continuation of the old PKI regime are busying themselves with unconvincing proposals purportedly to “combine” FIDO and PKI. In my view, it is inherently impossible to combine these two concepts without losing or cancelling out the essential features of each of these two fundamentally incompatible design concepts. The so-called proposal for combining FIDO and PKI is merely an effort to artificially prolong the shelf life of client authentication technology which relies on “globally identifiable” client certificate. Authentication with a key (such as NPKI client certificate) which can work across all websites is now a shockingly vulnerable concept. Had NPKI not been supported by the government, the industry in Korea would have been much more swift in learning about and realizing its vulnerabilities, and would have much sooner adopted better and newer alternatives including the industry standard such as FIDO.
An old technology of the late 1990s proving to be less secure than the cutting-edge security standards of the 2010s should not surprise anyone because the technology progresses and improves. But the problem with a government driven ‘standard’ is that once such a government driven regime is put in place, it becomes authoritative and remarkably difficult to get rid of. After nearly two decades, the Korean government, as well as its citizens, are still stuck with the outdated authentication concept and process of NPKI client authentication. Some of those who have vested interests in the continuation of the old PKI regime are busying themselves with unconvincing proposals purportedly to “combine” FIDO and PKI. In my view, it is inherently impossible to combine these two concepts without losing or cancelling out the essential features of each of these two fundamentally incompatible design concepts. The so-called proposal for combining FIDO and PKI is merely an effort to artificially prolong the shelf life of client authentication technology which relies on “globally identifiable” client certificate. Authentication with a key (such as NPKI client certificate) which can work across all websites is now a shockingly vulnerable concept. Had NPKI not been supported by the government, the industry in Korea would have been much more swift in learning about and realizing its vulnerabilities, and would have much sooner adopted better and newer alternatives including the industry standard such as FIDO.
South Korean government at long last accepted that they made a wrong decision in 1999. In 2018, the government prepared a bill to completely abolish the government accredited NPKI regime. The bill is now in the National Assembly. One hopes that it passes before the twentieth anniversary of NPKI regime in Korea. Governments in other countries should take the Korean NPKI episode as a cautionary tale about the importance of governmental non-interference with industry standard in the authentication and online identity technologies.
- “FIDO UAF and PKI in Asia – Case Study and Recommendations”, pp. 4-5. https://fidoalliance.org/wp-content/uploads/FIDO-UAF-and-PKI-in-Asia-White-Paper.pdf
- For a detailed discussion, see Keechang Kim, “Reform Proposals for the Korean Electronic Signature Act”, Journal of Comparative Private Law, vol 24, no. 4 (2017) pp. 1883-1930 (in Korean).
- Article 5(2) of E-Signature Directive 1999; Article 25(1) of eIDAS Regulation 2014.
- UETA, Section 7(d). Also see US Federal E-Sign Act (15 USC 7001) Section 101(a)(1), 101(a)(2).
- For a brief overview of the Korean NPKI certification service, see Keechang Kim, “Recent Changes in the Regulatory Landscape for e-commerce in South Korea”, 16 Asian Business Lawyer 78 (2015).
- The FIDO Alliance Whitepaper on Privacy Principles, (Feb 2014), p. 5. http://fidoalliance.org/wp-content/uploads/2014/12/FIDO_Alliance_Whitepaper_Privacy_Principles.pdf
- Supreme Court Judgment 2017Da257395, dated 29 March 2018.
- See, for example, https://fidoalliance.org/wp-content/uploads/FIDO-UAF-and-PKI-in-Asia-White-Paper.pdf (April 2018).

Professor Kim studied law at Seoul National University (LLB), Chicago Law School (LLM) and Cambridge University (PhD). He teaches contract, tort, e-commerce law at Korea University Law School. He is a Member of the Korean Bar Association, with frequent involvement (either as an arbitrator or as an expert witness) in international arbitrations. He is currently serving as an advisor to Culture, Media and Telecommunications Team of Legislation Research Commission of the National Assembly of Korea. His publications include Inconvenient Truth of the Korean Internet (2009). He has been leading the Open Web Movement in Korea, which advocates standard compliance in internet technology. He is currently a director of Open Net Korea, a charitable foundation promoting individual’s rights and freedom in the cyber space. His research interests are internet and the law, encryption and information protection technology and regulation of online transactions.
